Reveal & Control AI Data Exposure
Control what AI sees and secure it with confidence
Control what AI sees and secure it with confidence
AI tools like Copilot, ChatGPT Enterprise, and autonomous agents are now accessing enterprise data at scale, often without clear visibility or control.
Ray Security enables you to:
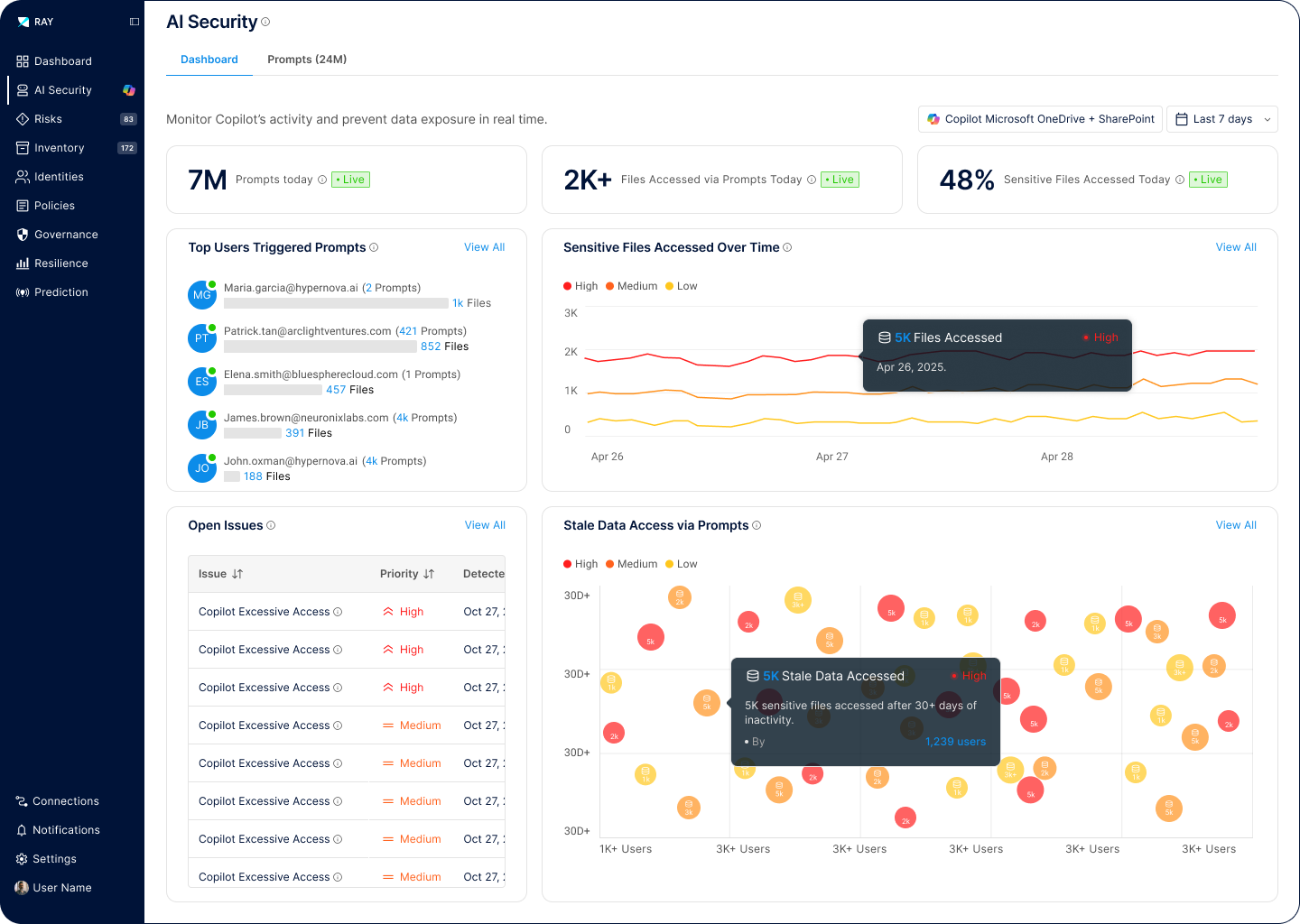
Define exactly what data AI tools and agents can access, based on sensitivity, context, and real usage.
Ensure AI agents operate within clear security limits. No uncontrolled access, no hidden data paths.
Prevent AI systems from exposing sensitive information in outputs, responses, or downstream actions.