The Data Security Platform Built for the Age of AI
Control how humans and AI agents access your data, before it becomes risk.
Control how humans and AI agents access your data, before it becomes risk.
| Use Case | DSPM | DSP | Traditional DLP | |
|---|---|---|---|---|
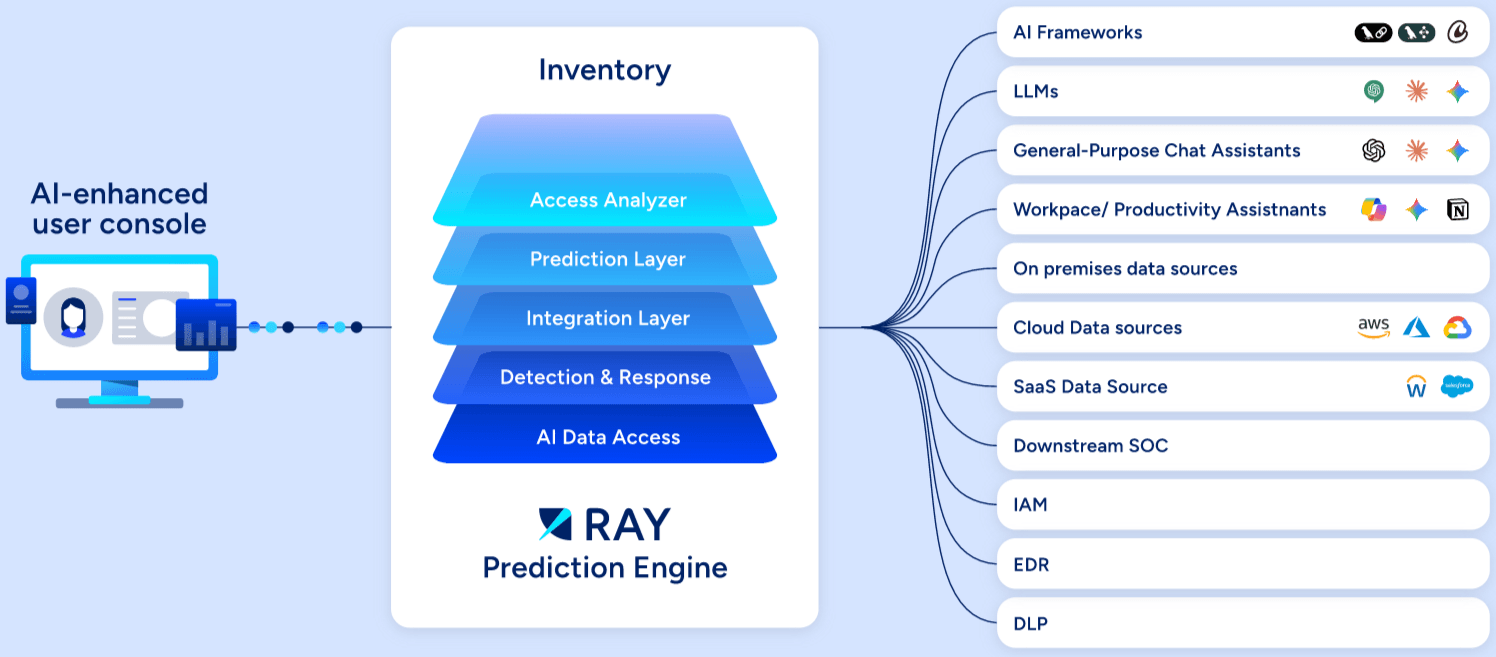
| Full data inventory and mapping | ||||
| AI Data Access Control | ||||
| Identify Shadow AI | ||||
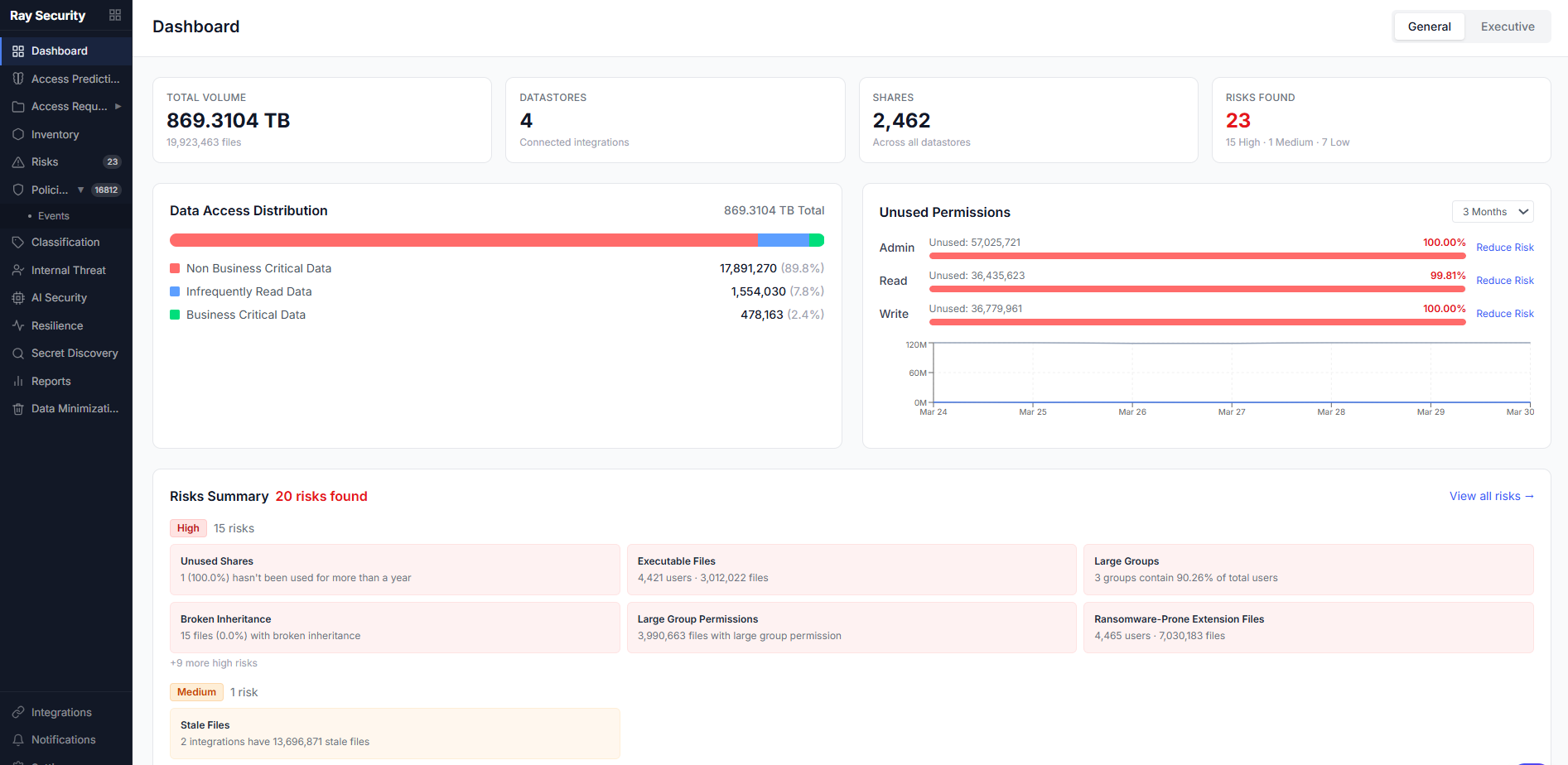
| Permission review and reduction | ||||
| Access anomaly detection and auto-mitigation |