Data Access Audit
& Investigation
Complete visibility into who touched what, human and AI alike, and when
Complete visibility into who touched what, human and AI alike, and when
When a breach, audit, or anomaly occurs, organizations must answer a simple question: who accessed sensitive data? Most cannot do so with confidence.
Ray Security provides full visibility into data access activity, by humans and AI, enabling teams to:
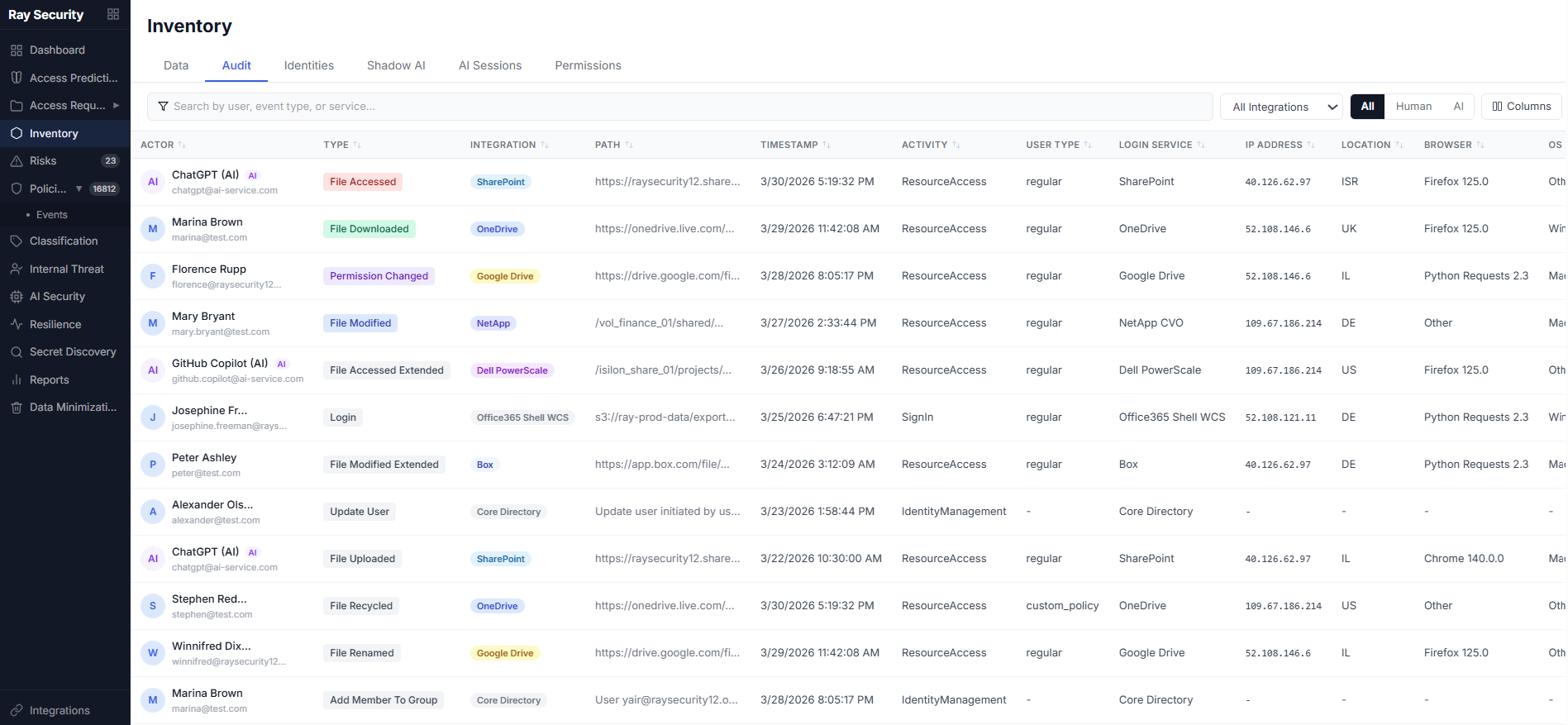
Identify every file accessed during a breach window, track the full scope of compromise, and provide board-level reporting with complete confidence.
Generate comprehensive access audit trails required by SEC, HIPAA, GDPR, SOX, and other regulations, without manual log aggregation.
Detect unusual patterns like bulk downloads, after-hours access, suspicious file interactions, or unexpected AI agent activity that indicate potential insider threats, compromised accounts, or unsanctioned AI operating outside policy boundaries.