AI Agentless Data Loss Prevention (DLP)
Bring data loss prevention into the AI era. Control data exposure and stop leakage across human and AI access.
Bring data loss prevention into the AI era. Control data exposure and stop leakage across human and AI access.
AI tools accelerate how data moves, but also how it leaks. Traditional DLP solutions react after data is already at risk.
Ray Security’s enables you to:
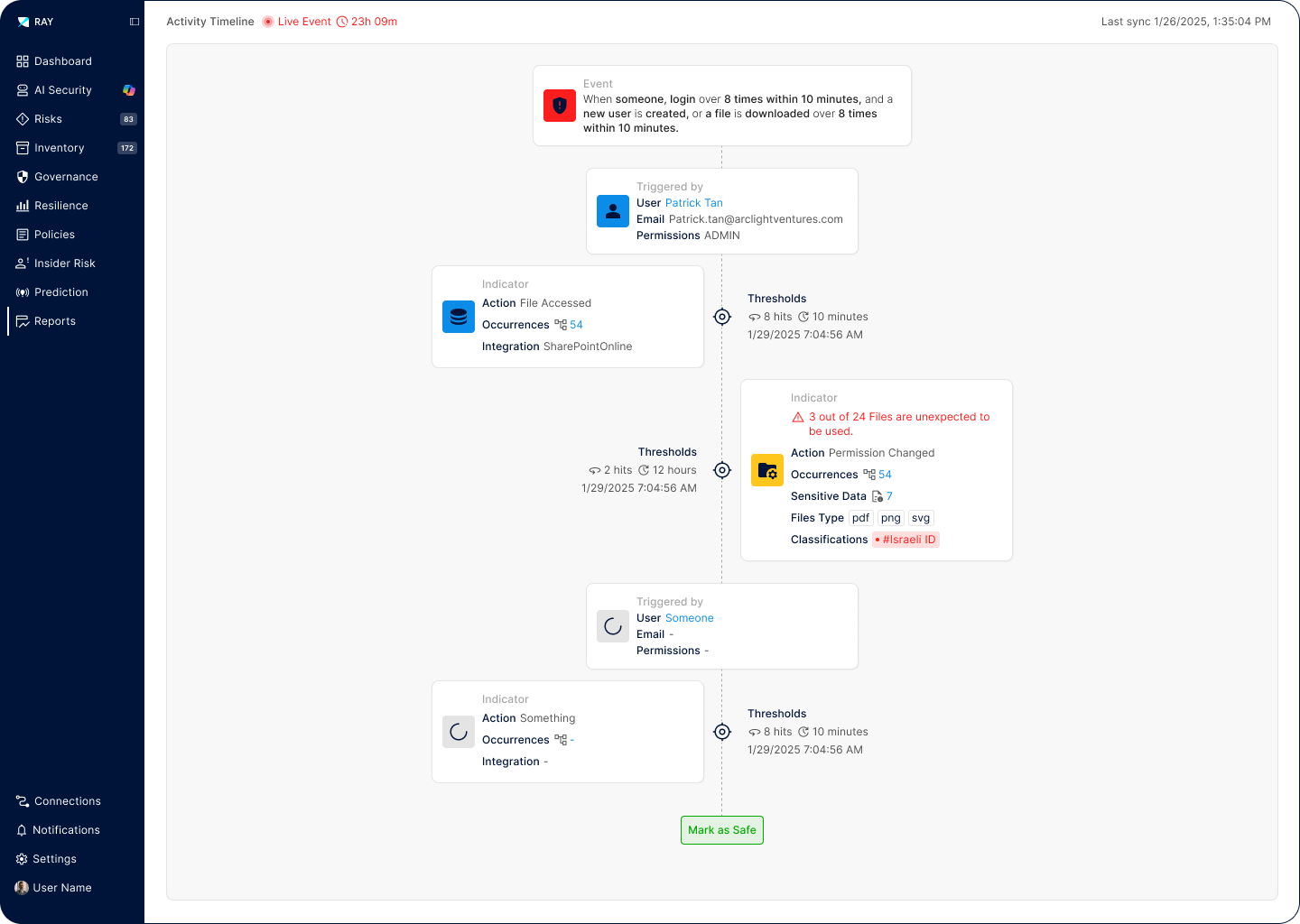
Our predictive engine identifies which data will be accessed, enabling proactive protection strategies that prevent unauthorized access before it occurs.
Track and monitor data as it moves across cloud, on-premises, and hybrid environments with comprehensive lineage and access justification for every interaction.
Automatically verify access justification for every interaction, human or AI, maintain privacy controls, and prevent unauthorized, uncontrolled, and unaudited data use across all environments.