Your Cloud Shared Files are a Ticking Time Bomb

Your Cloud Shared Files are a Ticking Time Bomb
Should we need to stop talking about “the cloud”?
For most organizations, the cloud isn’t a nebulous collection of AWS buckets or Azure instances, at least not to the people who actually run the business. To your Marketing Director, your Head of HR, and your Finance team, the cloud is simply a tab in their browser called Microsoft SharePoint or a shared folder in Google Drive.
It’s where your most sensitive intellectual property lives, breathes, and too often, leaks.
Consider the scale: 54% of all data stored in the cloud is now classified as sensitive (Thales Cloud Security Research, 2025), yet fewer than 10% of enterprises encrypt more than 80% of it. Furthermore, 55% of companies cite data privacy as an active challenge tied directly to misconfiguration, not sophisticated attacks, not zero-days. In other words, the problem isn’t that attackers are getting more clever; it’s that we keep leaving the door open.
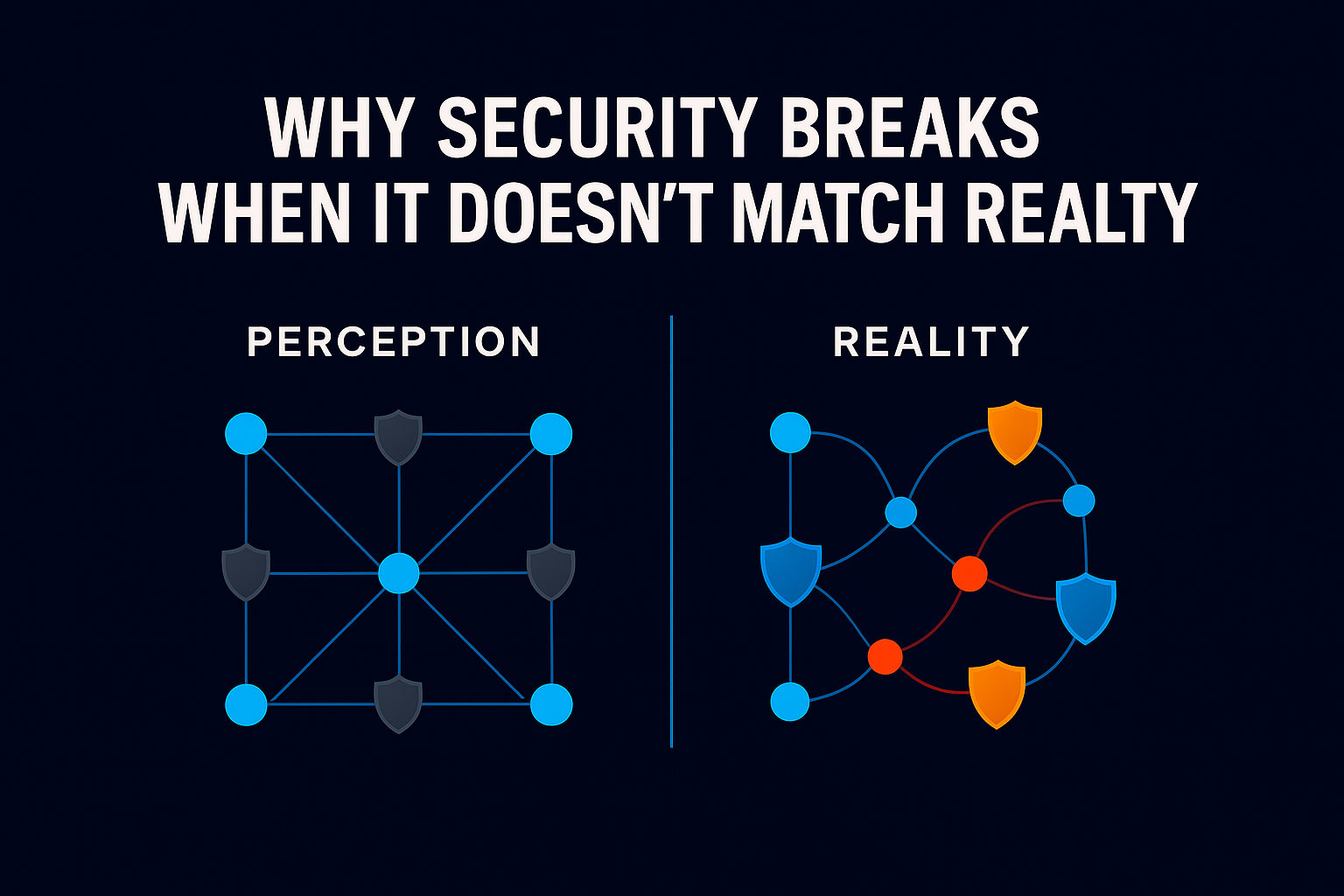
While security teams have spent years hardening the perimeter of their infrastructure, they’ve quietly left the internal connective tissue of the company wide open. We traded security for frictionless collaboration. In doing so, we created something far more dangerous: a collaborative blast radius that grows a little larger every single day.
The Eternal Life of a “Temporary” Link
Think back to a project you worked on last year. You likely created a folder in Google Drive, dropped in strategy documents, and generated an “Anyone with the link” shortcut to share with an external consultant.
The project ended. The consultant moved on. But that link? It’s still active.
In the world of SaaS, permissions don’t expire on their own. They accumulate. What starts as convenience becomes identity debt, a sprawling web of access granted “just in case,” but never revoked. In 2026, this isn’t just a hygiene issue; it’s a structural vulnerability.
If an attacker, or an automated system operating on stale permissions, gains access to a single legacy account, they don’t just see that user’s files. They inherit every “temporary” link that account ever touched. One identity becomes thousands of documents. That is the blast radius.
Seeing risk is not the same as reducing it.
In real-world deployments, we consistently see how large that radius has become. Across enterprise environments we work with, the number of unmonitored links that are fully open to the internet, meaning anyone, from anywhere, can access them without authentication, is on average nearly seven times the number of employees in the organization.
In other words, a company with 5,000 employees may be carrying 35,000 publicly accessible doors.
Why Visibility Is Only Half the Battle
Most modern security tools, including Data Security Posture Management (DSPM), are excellent at sounding the alarm. They can scan your SharePoint environment and tell you that you have 50,000 at-risk sharing links.
But then what?
You can’t simply kill them all. Do that, and you’ll break active projects, interrupt operations, and spend weeks answering angry emails from leadership. This “fear of breaking things” is exactly why most organizations allow their exposure to persist. They have visibility, but they lack the ability to act safely.
And so, the blast radius continues to expand.
From Static Permissions to Living Access
The root problem is that access is treated as permanent. Traditional security models ask a binary question: Does this identity have permission? They don’t ask the more important one: Is that permission still being used and does it still make sense?
A sensitive SharePoint file that hasn’t been opened by a specific user in three months isn’t empowering productivity anymore. It’s just sitting there, quietly widening your attack surface. This is the gap that traditional DSPM and DLP tools weren’t designed to close.
At Ray Security, we call this Usage-Aware Remediation.
Instead of treating permissions as permanent yes-or-no decisions, we correlate data sensitivity with actual usage. If a user, group, or public link hasn’t touched content in 90 days, that access path is no longer a tool. It’s a liability.
This makes it possible to surgically remove “dead” access without disrupting the work that matters. The focus moves from “who technically has access” to “who is actively using it,” allowing organizations to prune exposure continuously, before it turns into breach fuel.
The Hidden Cost Nobody Is Counting
Authority without constraint is not innovation. It’s an unmanaged risk with a productivity veneer.
The hidden cost of permission sprawl becomes painfully visible when a modern AI assistant surfaces sensitive data to the wrong person because of an “org-wide share” forgotten three years ago. These legacy mistakes lead to regulatory fines and incident response bills that quickly erase the efficiency gains that justified using the cloud in the first place.
Machine-speed collaboration now defines how modern enterprises operate. That reality demands machine-speed governance. The leaders who win this next phase won’t be the ones deploying the most tools. They’ll be the ones who can prove they still control where their data lives, and who can shrink their collaborative blast radius without slowing the business down.
Next: A Monday-Morning Checklist for Shrinking Your Blast Radius
In our next post, we’ll walk through a practical, step-by-step checklist for auditing and remediating SharePoint and Google Drive exposure, prioritized by risk, safe to execute, and designed to fit into a working week.