The Shadow Insider – When AI Agents Touch Your Data

The Shadow Insider – When AI Agents Touch Your Data
Some data security controls can tell you who accessed sensitive data, as long as “who” means a human. In the age of agentic AI, that’s no longer enough.
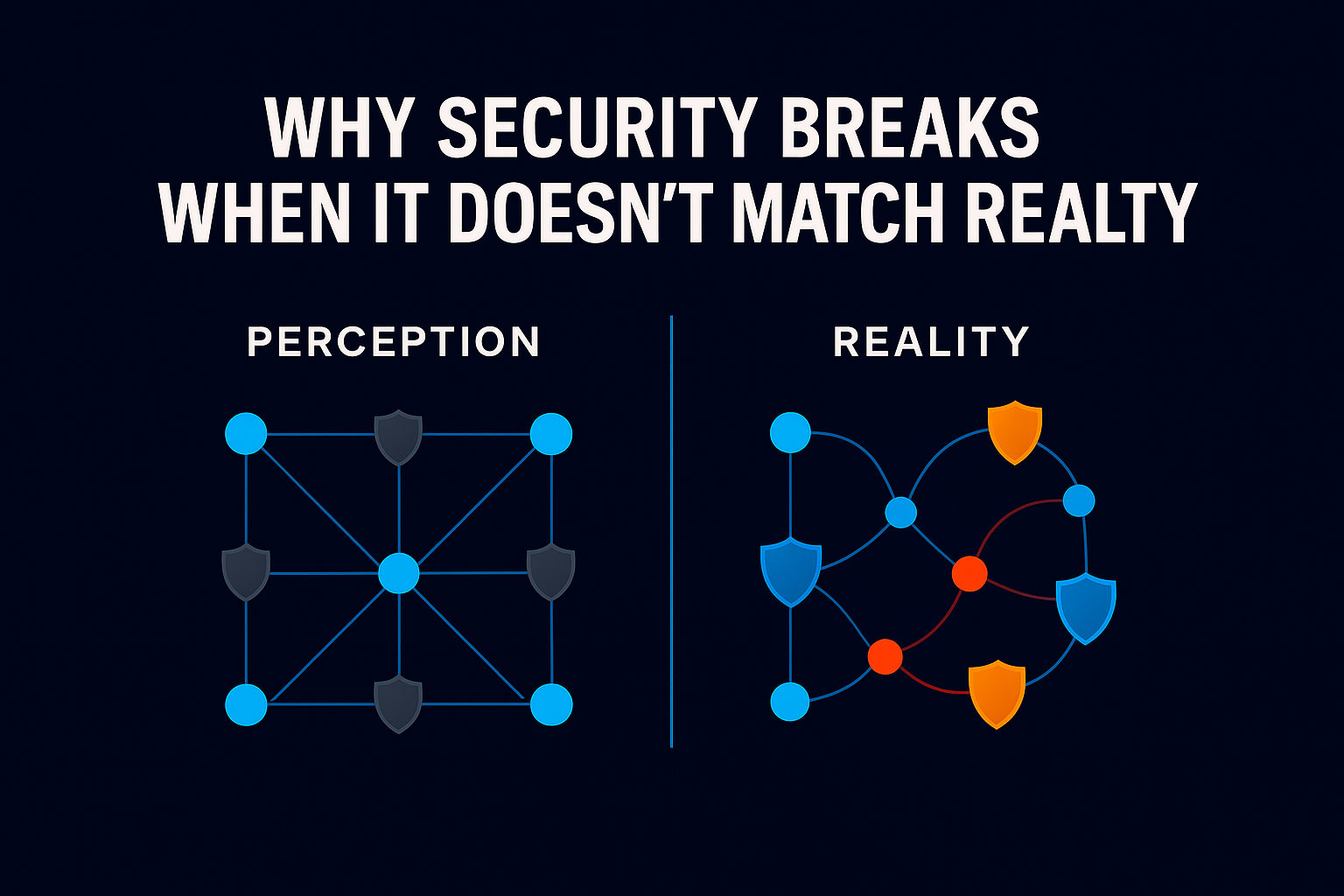
For years, when a security team investigated a data incident, the first question was simple: who touched the data? The assumption was obvious, the answer would always be a person. An employee, a contractor, a partner with overly broad access., a server, service accounts.
That assumption is breaking down. And the security programs still built around it have a growing blind spot at their center.
AI agents are now embedded across enterprise operations. They retrieve documents, query databases, summarize sensitive records, and trigger cross-system workflows, often without a human in the loop. They are, in effect, a new kind of workforce: digital employees operating at machine speed, around the clock.
The scale of the problem is significant. Research from Obsidian Security found that AI agents move 16 times more data than human users – in one case, a single agent downloaded over 16 million files while every other user and application combined accounted for just one million.
The problem is that most organizations’ security programs were never designed to watch them.
The newest insider in your organization might not be a person at all. It might be the agent quietly working in the background.
A Visibility Gap That’s Already Here
Traditional data security tools were built around a static model: identities, permissions, repositories. They tell you where sensitive data lives and which users technically have access to it. When humans were the primary actors, that was enough.
Agentic AI changes the model fundamentally. Agents move data dynamically and not deterministically across systems, often far beyond what any specific task requires. They operate through shared service accounts and API keys, making attribution difficult. And because they don’t only execute instructions but rather they can also make choices, they’re not doing exactly what they were designed to do. They can do way beyond what they have been instructed to do. They can make choices and their choices can be inconsistent, context dependent, exposed to what they have “heard” and can dramatically change from run to run.
The industry data reflects a security posture that hasn’t kept pace:
- 79% of enterprises have blind spots where agents touch data the security team cannot observe. (Akto, 2025)
- 92% of organizations lack confidence that their IAM tools can manage AI agents and non-human identity risks. (CSA / Oasis Security, 2026)
- 28% of security professionals believe they can prevent a rogue agent from causing damage, in systems many have already deployed. (Keyfactor / MSSP Alert, 2026)
What Ray Security Does Differently
Ray Security extends visibility to a new class of actors in the enterprise: AI agents.
When security teams investigate how sensitive data is used, Ray Security shows the complete picture, including both human users and autonomous systems operating on their behalf.
Ray Security provides control beyond the traditional security layers: it continuously monitors real data usage across the environment, identifying Agentic AI activity from data access patterns alone. By revealing which agents access sensitive datasets, how frequently those interactions occur, and which human teams ultimately own the workflows involved, Ray Security lets security teams regain control. By correlating human and non-human activity around the same data, Ray provides a unified view of how information actually moves across the organization.
The result is an Agentic AI Data Control as well as a true audit trail that reflects how modern enterprises operate today: people and AI agents working together, interacting with the same data.
The Question Hasn’t Changed. The Answer Has.
The organizations that will succeed in the agentic era aren’t the ones that slow down AI adoption.
They are the ones that adapt their security programs to match how work is actually getting done, with visibility and accountability across every actor interacting with their data.
Because in the modern enterprise, the answer to “who touched the data?” may no longer be a name on an employee directory.
It might be the AI agent that quietly ran the workflow.