5 Steps to Shrink Your Blast Radius

5 Steps to Shrink Your Blast Radius
Your team generated 4723 “Anyone with the link” shares in the past 3 months. How many of them are still active now?
The challenge for security leaders isn’t a lack of motivation. It’s the fear of breaking the business in the process. You can’t just revoke everything. You need a surgical approach.
Here is a five-step checklist you can start executing this Monday to reduce exposure without interrupting the workflows your teams rely on.
1. Audit Your “Anyone with the Link” Exposure
The most dangerous permission is the one that requires no identity at all.
- THE ACTION: Run a report for files shared with “Anyone.” In SharePoint, navigate to SharePoint Admin Center → Reports → Sharing. In Google Drive, go to Admin Console → Security → Access and data control → File Exposure Report.
- THE FOCUS: Don’t try to fix everything at once. Start with content labeled Financial, PII, or Legal.
- QUICK WIN: For sensitive folders, move sharing from “Anyone” to “Specific People” or “Internal Only.” This alone can dramatically shrink your external blast radius.
- HOW RAY SECURITY HELPS: The predictive data security platform finds the people who used which link and creates links that allow only these people to use it.
2. The 90-Day Dormancy Purge
Permission without activity is just risk waiting for a reason.
- THE ACTION: Identify external collaborators (contractors, partners, former agencies) who haven’t logged in or accessed files in 90 days.
- THE FOCUS: If they haven’t touched a file in three months, they don’t need standing access.
- QUICK WIN: Disable those accounts. This shifts security from permanent to purpose-bound.
- HOW RAY SECURITY HELPS: The predictive data security platform removes access to anyone that didn’t use a link/permission after a certain time.
3. Audit Third-Party OAuth App Grants
Years ago, someone in Marketing approved a social media tool. Someone in Sales authorized a CRM integration. Each was granted org-wide read/write access, and most are still sitting there today.
- THE ACTION: In Google Workspace: Admin Console → Security → API Controls. In Microsoft 365: Azure AD Portal → Enterprise Applications. Review apps with “Files.ReadWrite.All” permissions.
- THE FOCUS: If an app hasn’t been used in six months, revoke its access.
- QUICK WIN: Revoking “zombie” integrations is the fastest way to close a massive, invisible exposure surface.
- HOW RAY SECURITY HELPS: The predictive data security platform can revoke access to inactive apps.
4. Hunt for Shadow Drives
Data rarely stays where you expect. Employees often download files from SharePoint and re-upload them to personal drives because it feels easier. Once data leaves your managed environment, your blast radius is out of control.
- THE ACTION: Use your CASB or DLP solution to flag download-then-upload patterns, specifically large downloads from managed storage followed by uploads to unmanaged platforms like personal Dropbox or iCloud.
- THE FOCUS: This isn’t about blame; it’s about identifying where your data is drifting.
- QUICK WIN: Implement alerts for abnormal download volumes and automatically require re-authentication or approval for large exports of sensitive data.
- HOW RAY SECURITY HELPS: The predictive data security platform monitors and prevents large downloads
5. Move Toward Usage-Aware Remediation
Manual permission management doesn’t scale. You cannot out-click a workforce of thousands.
- THE ACTION: Evaluate systems that automate governance based on actual usage patterns, not static permission lists.
- THE FOCUS: The goal isn’t fewer permissions. It’s smarter permissions, access that reflects how people actually work, not what they were granted years ago.
- QUICK WIN: Usage-aware systems allow you to surgically remove “dead” access without disrupting active work.
- HOW RAY SECURITY HELPS: The predictive data security platform correlates data sensitivity with actual usage. If a user or public link hasn’t touched sensitive content in 90 days, that access path is no longer a tool, it’s a liability.
The Goal: Continuous Pruning
Security in 2026 isn’t a one-time cleanup. It’s a living process, more like gardening. If you don’t continuously prune legacy access, the weeds eventually take over.
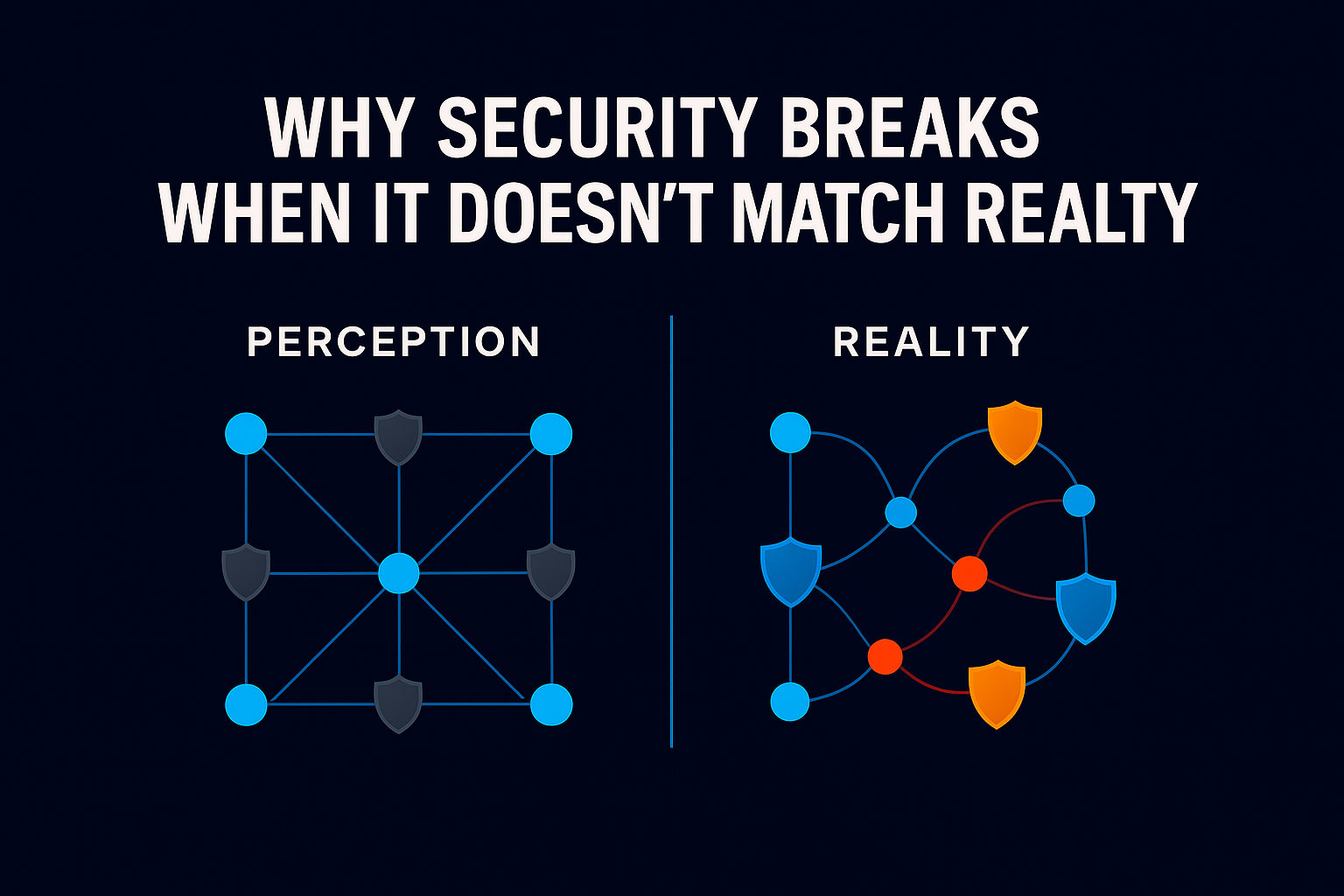
But there is a new “accelerant” making those weeds dangerous: Agentic AI. Unlike standard chatbots, AI agents have the power to execute tasks, move files, and use tools. When you deploy these agents, they inherit every “forgotten” permission and “Anyone with the link” share you’ve failed to revoke. A single misplaced folder isn’t just sitting there anymore, it’s now an active resource for an automated agent to summarize, move, or leak.
One final question for every CISO and IT leader: As automation and AI-driven workflows become embedded across your organization, are they inheriting your business intent, or just forgotten permissions?
If the answer is “I don’t know,” it’s time to move beyond visibility and start remediating.